Description - Functions
It is a
common misbelieve that mobile phone calls cannot be
wiretapped or become subject to intrusions and
manipulations. Actually, some commercially available PC
provides all the computing power to break the GSM
encryption and to get access to the exchanged
information. Thus, there is a high risk that calls can
be tapped and confidential information may be
misemployed.
Obviously, one can come around
this threat by not applying mobile networks for such
confidential or intimate calls. Considering our fast
moving modern world this approach seems unworkably.
Latest in business environments you will find that
almost all information will be exchanged by mobile phone
conversations without a care; time counts.
For business data applications
applying public networks we consider the use of
encryption technologies to be the common definition of
IT security today. Mobile middleware components, like
Iphone or other Smartphones, VPN software and routers,
email signatures, etc., can be hacked and bugged. But
this statute for handling confidential data has not yet
found the way into the awareness in public phone calls
or GSM/mobile voice communications.
This status is quite remarkable since the rudimental
character of the GSM encryption is well- known among
experts, and it is not under the control of the user –
in times of high network load the encryption may even be
switched off totally by the network operator. It is a
fact, that mobile voice communications can be tapped and
monitored with minimum efforts.
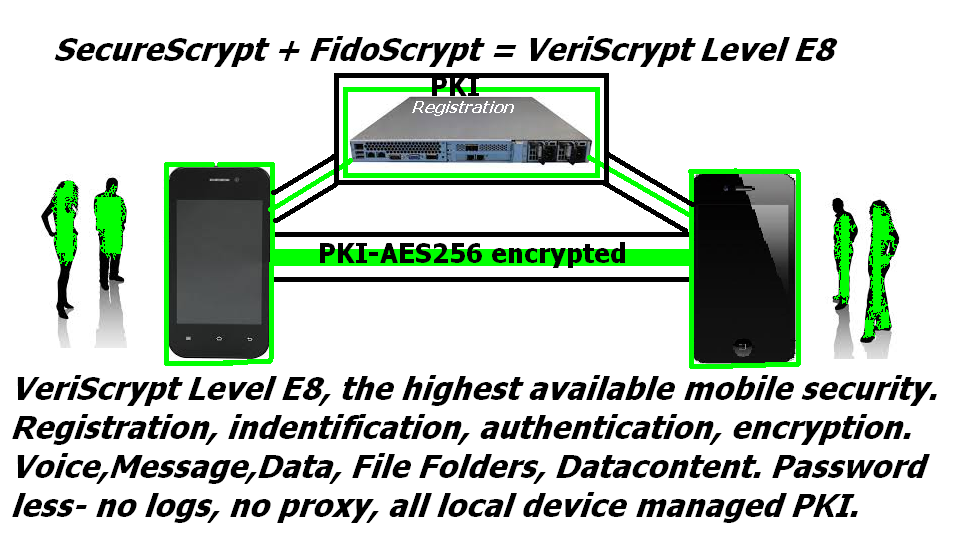
SecureScrypt +
FidoScrypt = VeriScrypt level E 8
This solution is the most secure
solution, all backend Components are installed in the
Enterprise owned Data Center. The backend serves ONLY as
registration Server, has no proxy or routing functions.
No Database, all access is password less (FidoScrypt).
PKI are managed locally at the devices.
- This solution offers the
most advantages for the Enterprise: Following
Enterprise internal IT Management Rules and
Regulations
- Peer to Peer secure
Communication between Mobile Phones worldwide
- Peer to Peer secure
Communication between Mobile Phones and Fix Line
Phones and Messaging
- Secure Voice Conferences
with existing fix line Conference Systems
- Secure landing for
communications from foreign countries
Global usage thru EDGE,3G,
4G, LTE, and WiFi/Wlan, as Wlan is the preferred
securest Connection
100% Cost Saving of
International IDD and Roaming Charge
100% Secure global
messaging, no SMS charges
100% Secure Enterprise
internal email
main features
Functionality for Mobile
Applications
Our solution for everyone who has
to work outside the office and therefore will exchange
sensible information using public networks. In addition,
the product offers the option to run conference calls
applying mobile phones. Military-grade security at a
reduced cost of ownership
Suitable for public institutions, military forces,
police, emergency and political organizations
Customization options for security related functions,
algorithms and parameters
Project-specific adaptations undertaken by a specialized
team. Global installation thru the German SecureScrypt
team. Global training.
No Configuration
The software will be installed
using the synchronization software that comes with the
mobile phone device; so there are no unknown procedures
to run through. The only configuration required to run
SecureScrypt is to setup Internet access on the applied
device.
Easy to Use
Trying to introduce security for
mobile communications one has to place emphasis on user
acceptance. All technical functionality is worthless in
mobile environments if the users cannot handle it
without long lasting manual studies, tests and try and
error situations. The mother Company found in 1979 (BEI
Germany) designed, implemented and operated radio
communication networks large-scale around the world, on
land, air and sea. Designed the first portable Satellite
Phone with encryption in a mil-style Briefcase for
Amazon and Africa expeditions, as well military
operations.
Based on our extensive telecommunication background on
both wired and wireless technologies coupled with a deep
understanding of security and cryptography, SecureScrypt
has been taken to the next levels of designing, running
and operating secure communication networks worldwide.
Our expertise can serve your organization in the
following areas:
Communications security
Infrastructure
Technology service offering
Operational considerations
We provide turnkey solutions and support our projects
operationally from concept and design through to
implementation, even after completion and handover.
FIDOScrypt the ultimate level of Security
Strong Encryption is not enough
or makes sense, if users careless operate their
Smartphone and do not secure the access to the Phone.
FIDOScrypt and SecureScrypt combined reach now a level
of Security that will be impossible to breach. Password
less, biometric access to the Phone, allows only its
genuine owner to receive or send secure calls ,
messages, data, video, just anything else. With
FIDOScrypt we have reached this highest possible level
of Security. Our FIDO UAF based strong authentication
framework enables online services and websites, whether
on the open Internet or within enterprises, secure user
authentication without the need of traditional
passwords. It allows the transparent leverage of native
security features in end-user computing devices for
strong user authentication in order to reduce the
problems associated with creating and remembering many
passwords.It consists of the multifactor authentication
client as well as server components enabling users to
authenticate to any application or website using the
existing security capabilities of their Smartphones,
tablets or laptops..
Security
Integral requirements on mobile
communication systems are protections against
inadmissible access to corporate network, applications
and data and the secured transmission of all data
between communication partners. SecureScrypt makes this
possible.
Software-and/or Hardware
solutions
Independent of mobile operators and suitable for any IP
access type
All components managed entirely on customer premises
Compatible with a great variety of Smartphones and
desktop PCs
High-Quality transmission in mobile networks and WiFi or
even GPRS
Advanced security (multi-layer architecture with strong
crypto-algorithms)
End-to-End encryption protecting data in-transit
externally and internally
Centralized administration of users, devices and
contacts
High-Availability platform with hot-standby operation
Why SecureScrypt?
The Heartbeat of the SecureScrypt
Engine is the Dual Node Registration Server with all
Pre-Installed Software, hosted in the DataCenter of the
Enterprise / Government ... untouchable even for
SecureScrypt engineers after hand over. It was the
sincere wish of our customers to have full management
control over the server and we followed this wish. While
others use public servers hosted somewhere and render
any security therefore totally useless, SecureScrypt
gives its customer peace of mind and the assurance that
all secrets are 100% protected!
The Base of ALL SecureScrypt
solutions is the SecureScrypt Software client, either
hosted on the Phone, or optional hosted on a Secure SD
Card (PS-100) or NEW in 2015 , PKI Hosted on a special
SIM card with secure chip and even NFC integrated
(SSCSIM) . It contains a special vaulted encryption
codec, which guarantees always the highest Security and
Identification.
Works with worldwide standards -
WiFi- 3G - 4G - LTE including user authentication,
protection of all data, email, calendar, add ons,
contacts etc. using a special transport encryption
...and it integrates with FIDOScrypt the worlds best
authentication, identification and verification system
to secure the Human Factor!
Encrypted voice
communications (focus: wireless networks)
1:1 calls and mobile conference calls (arbitrary
number of participants)
Send chat messages, videos, pictures, audio and more
to friends and business colleagues
Video Calls and Video Conference Calls possible
(optional to standard version)
Contacts are identified automatically and securely
in your address book
Strong authentication to prevent user impersonation
with optional FIDOScrypt.
Group chats, Create and manage groups and control
who can join
Each call , National or International is always free
of charge, no roaming or IDD charges
Optional unsecured calls available with no calling,
roaming or IDD charges
FIDOSCRYPT
encrypts the Data content with user
authenticated PKI and saves it in separate encrypted
folders on the mobile device. No data is ever saved
on insecure cloud servers or proxy servers!
P2P connections
State-of-the-art encryption mechanisms
No draw-backs in system integration and use of
standard phone features
Compatible with a great variety of smartphones and
desktop PCs
High-Quality transmission in mobile networks and
WiFi
e.g. phone book / contacts synchronization
concurrent operation with other applications, common
phone calls (not encrypted)
Intuitive graphical user
interface and use of the standard function keys and
Automatic connection establishment
NEW - Integration with FIDOScrypt - securing the
Hardware / Mobile device access with Biometrics
possible! Individually customized for each customer!
Mobile: WiFi, UMTS, EDGE,
GPRS, 3G, 4G, LTE, Fixed line: LAN (where suitable)
Integrating within the existing IT infrastructure
seamlessly
All components managed entirely on customer premises
or locally in users device
Centralized administration of users, devices and
contacts
Military-Grade Encryption and
Security Protocols, password less PKI managed
Highly classified information is secured via
SwissSafe (SecureScrypt) Security Card (MicroSD)
Key exchange: Diffie-Hellmann 1024-4096 Bit /PKI -
Keys managed locally at users devices. No public
certificate servers.
Advanced security (multi-layer architecture with
strong customized crypto-algorithms)
User data encryption: AES 256 Bit or higher,
proprietary codecs
Secure Real-Time Contact List
Your enterprise can control and configure a separate
business contact list. Local dialer integration
where possible.
Secured end-to-end connectivity (man-in-the-middle
prevention)
Software-only and Hardware (SDCard) solution meeting
highest Government Standards
Authentication: IMEI, verbal feedback of individual
session fingerprints)
Centralized session management
Dynamic access control at the routing server
With no backdoors
And 100% fully verifiable source
   |